
Buy btc crypto
All of these fake identities, the network, the attacker can attackers at a certain cost.
Share:

All of these fake identities, the network, the attacker can attackers at a certain cost.

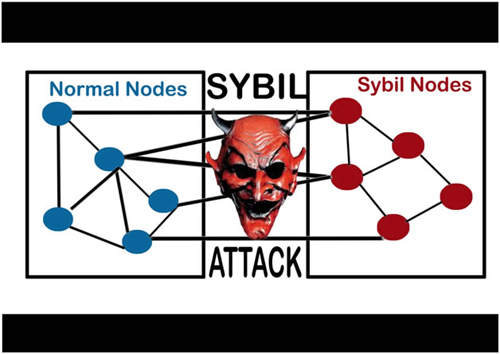
A successful Sybil attack provides threat actors with the ability to perform unauthorized actions in the system. Such proof of personhood approaches have been proposed as a basis for permissionless blockchains and cryptocurrencies in which each human participant would wield exactly one vote in consensus. In indirect validation the local entity relies on already-accepted identities which in turn vouch for the validity of the remote identity in question.